The material appearing in these pages is intended for informational purposes and should not be considered legal advice or used as such.
Q. What can schools do during the COVID-19 crisis to make vulnerable children safer when isolated at home?
A. A number of resources are available from multiple sources on the COVID.ICMEC.org page. These resources support the following guidance:
- Let staff, parents and students know that school policies are in place during this time. Issuing an addendum to your child protection policy is one way to do this. This may include a reminder about staff codes of conduct, mandatory reporting, and expectations of participation and attendance. It can also include an appendix for local and online contact information for child advocates and service providers.
- Start or continue a central record of students previously or newly identified as vulnerable with access limited to designate and deputy. Include known or suspected child protection concerns or those with safety plans for neglect, witness to violence in the home, or physical, emotional or sexual abuse risks related to a variety of factors including those arising from the crisis.
- COVID-related additions to the record can include a risk assessment and record of student details such as: where the student is located; who is in their residence; whether caregivers are working outside or inside the home; the child’s access to the Internet, devices, and green space; and health risks associated with the work or visitation of a non-resident parent.
- Your COVID section should include a place to record success/failure of telephone checks, visual checks and virtual learning participation with a date and who made contact. There is a danger of children going missing from education at this time.
- Recordings of synchronous learning or visual checks should be used only to mitigate child protection risks. Those recorded should be notified of this record. Data protection guidelines may require documentation of purpose and evaluation of how long this record is retained, depending on assessed vulnerability. See Adapting to New Learning Environments for more.
- Keep lines of communication open. Consider adding a dedicated, monitored email and/or text phone number for named or anonymous reporting. Ensure faculty, parents, and students know the reporting options and have opportunities to share their fears and frustrations. Provide information and referrals in a targeted approach based on requests or identified needs.
- Finally, prioritize wellness over academic goals. Continue to deliver social-emotional learning and abuse prevention education to students, such as lessons on unhealthy relationships, reporting to trusted adults, seeking help online, and features of online luring or grooming for the purpose of sexual abuse and exploitation.
Q. My school or organization needs a child protection policy for accreditation. Where do we start?
A. Your policy tells staff, parents and your community how you are going to protect children in your care. Look at the requirements of your accrediting agency. If they are signatories to the new standards for child protection the essential questions will give you a place to start. Also, see our quick start links and Child Protection Policy template or downloadable checklist for developing a child protection program. This includes links to sample policies and supplemental policies as well as checklists, forms and flow charts for helping you develop supporting procedures that fit your organization and location. Child protection policies and codes of conduct should be publicized within the school community, posted, and reviewed and signed during induction training. Policies and supplemental policies should include the creation date and the last date reviewed which typically happens annually. Community and student opinion should be included in the creation process. Policies should be made available in child-friendly language, simple English, and language/s understood by community.
Supplemental policies address: safer hiring, supervision, whistleblowing, acceptable use policies (AUPs) including photography, social media and digital communication, dual relationships, trip/travel, intimate care (diapering, toileting support), changing/locker room policy, data protection, peer abuse, and other child protection related topics.
Q. What should a peer-on-peer abuse policy include?
A.Peer-on-peer abuse is any form of physical, sexual, emotional and financial abuse, and coercive control, exercised between children, and within children’s relationships (both intimate and nonintimate), friendships and wider peer associations. Policies related to student harm may be added to current bullying or disciplinary policies or may fall under your overall child protection policy. Whether the peer abuse policy is separate or included in other policies it should be developed with the input of staff and students. It should provide clear guidance that is understandable to adults and children about how you will prevent, identify, and address peer abuse. In all cases stigma should be avoided and the age of the child and the harm caused should be considerd in the response.
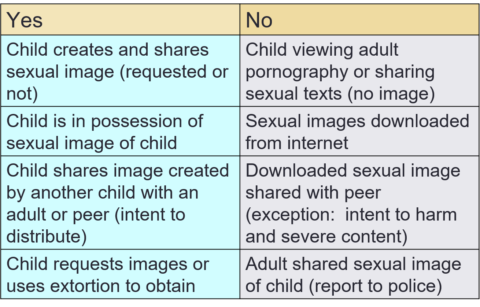
With respect to the sharing of sexual images this policy addresses:
The peer abuse section or policy should include: definitions of contact and non-contact abuse; definitions of developmentaly expected as opposed to inappropriate and harmful or problematic sexual behavior (HSB/PSB); clear internal and external referral pathways; contextual safeguarding response including risk assessment and safety planning for both child who was harmed and child who harmed; and how proportinate engagement with local authorities will take place. It should include a statement on avoiding the criminalization of children, proportionate response, and information about local laws related to age of consent, age of criminal responsibility, and creation and possession of sexual images of children. Zero tolerance for abuse and harrassment, reference to acceptable use of technology guidelines, and current codes of conduct should be clearly stated.
All members of the community should understand the tenants of your student abuse prevention curriculum and how exchange of non-consentual sexual images should be addressed. Find School Policies and additional guidance in the Incident Response, peer abuse section.
Q. How do I prepare staff to protect children or youth in our care? Who should be trained and when?
A. Intake and regular professional development training should be provided to all staff roles with access to children, including non-teaching staff, volunteers, after school supervisors, and security guards. Parents and caregivers should be offered training or information in conjunction with publicizing your school child protection policy and Code of Conduct, and be introduced to student safeguarding curriculum by grade level. School heads, child protection designates or team members, and designated school board members need additional training.
View the phases of implementation in Your Child Protection Training Plan. Your staff training should include: a review of your policies and procedures including reporting obligations; definitions of abuse and neglect; familiarization with offender patterns including grooming; identification of vulnerable students; signs and symptoms of abuse; handling disclosure appropriately; reporting procedures for violations of school policy and codes of conduct; and trauma-informed care of abuse victims. Training should address cultural considerations of host country, local reporting laws and obligations, and the strong emotions that these topics can evoke.
Induction training and annual professional development training may be in-person group training, in-person individual training, web-based self-paced or group training, or may combine elements of these with written resources and online or in person discussion. Course should be scenario-based with decision-making practice. Staff should be given an opportunity to address their concerns and other strong emotions in a supportive environment. For more information on the contents of comprehensive child protection training see the Training Checklist.
Q. How do we implement the accreditation requirement to teach our students about abuse? What does student prevention education need to cover?
A. Review the curriculum resources which include recommended characteristics of effective prevention education, safeguarding curricula scope and sequence, samples of best practice and other resources. An effective school-wide child protection curriculum contains research-informed instructional methods, developmentally appropriate content, and family outreach. Be sure the prevention curriculum you create or purchase is scenario-based, interactive, and spirals so concepts are built upon year after year. Prevention curriculum covers social-emotional learning (referred to variously as SEL, SRE, CSE, or PSHE) and e-safety or internet safety education (ISE). Scope and sequence samples for both curricula are provided in curriculum resources.
Social-emotional and e-safety curricula are rooted in the school’s child protection policies and e-safety policies and procedures. Both strands should build student self-respect, confidence, resilience, and decision making skills. Purchased or created lesson plans should include teacher support and be part of a whole school approach. All staff including non-teaching staff, volunteers, tutors, coaches and after school activity supervisors should share consistent vocabulary and model good conduct.
Q. Doesn’t publicizing our safeguarding policy with the wider community invite a lot of problems?
A. Your child protection policy and staff code of conduct defines expectations, dispels cultural stereotypes, improves parenting, helps adults identify inappropriate behavior and symptoms of abuse, and creates an ethos of prevention. It enlists all members of the community to work collaboratively to protect children in your care. Search your school site for child protection language. If no results are found, what message does that send to prospective employees or families about your priorities?
Telling prospective employees that your school aspires to the highest standards of child protection and adheres to protective recruitment and employment standards is a requirement of accreditation. These actions alone will not prevent abuse from occurring, but may warn off unsuitable candidates. All preventative measures work together and must be part of the wider school ethos.
Q. What’s the difference between the crisis team, the child protection committee and a child protection response team required for accreditation?
Most schools have a crisis team made up of senior leadership. When schools take on policy writing, often a committee is created for this work. New accreditation standards for child protection refer to child protection response teams. See the table below for the overlapping and distinct requirements and responsibilities of these groups.
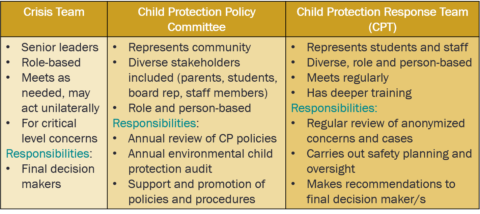
Schools should consider size, campus layout and the qualities of staff members in various roles when forming a child protection response team. Separate teams for split campuses or for different divisions may be needed. A representative of the response team should be on the policy committee and participate in audits. Typically this is the child protection designate (CPD) and/or deputy. The response team recommends changes to policies and procedures in light of concerns or allegations.
Well trained, diverse response teams provide the best outcomes for children and those accused of harm. They are transparent in process but prioritize confidentiality. The best interests of the child is always at the center of their work. For more information on forming teams and the role of child protection designates see Prevention and the AISA Guidance for Teams and Internal Reporting.
Q. How should school assist staff involved in a child protection concern?
A. The process for allegations against adults should be explained in the school’s child protection policy and made explicit to staff in interviews and intake training. Violations of the staff Code of Conduct are grounds for dismissal. When a child protection concern is raised, the school will generally conduct an internal review or risk assessment. This is done by the child protection response team, senior leadership, or an outside expert or adviser. During this process the child/children involved are protected by safety planning and any adult involved in the allegation of inappropriate conduct is removed from contact with children and may secure their own lawyer. A colleague or HR staff member should be designated as the representative of the accused staff member to keep them updated on the allegation protocol review process. Confidentiality should be maintained during the process. All allegations, findings and decisions should be documented and securely retained in the central record.
Q. What should our central record of child protection concerns include?
The single central record (SCR) of child protection concerns contains date/time of incident/disclosure, date/time of report, name and role of person concern reported to and contact details, name/role of person making report and contact details, names of all involved including witnesses to an event, what was said/done and by whom (in child’s own words if from disclosure), and any action/s taken to address the concern. These may include mandatory reporting, safety plans, referral, disciplinary action, corroboration, supervision or policy changes, risk assessments, etc. Accountability for disciplinary or supervisory actions, and/or follow up triggers should be indicated. Any justification for not reporting to parents and local authorities should be clearly documented.
The record is started as soon as any concern arises, however small, whether ‘formally’ reported to staff or not, and includes anonymous allegations. It may be legally required that this record be retained beyond a child’s enrollment and/or an employee’s employment for a specific period of time. In the absence of legal guidance it’s best to do the most the law allows rather than the least the law requires. If local privacy restrictions are rigorous, be aware of exceptions for child protection information, such as in EU GDPR legislation. Your policy for retaining substantiated child protection allegations in student and employee files may be determined by local statutory guidance, your insurer, or your inspection or accreditation agency.
These confidential records should be accessible only by those with a need to know (sign out tracked and password protected). The child protection log is kept separate from personnel files, cross referenced or linked in child’s file and staff personnel file, where applicable. If an allegation is deemed malicious, the record should be deleted and supporting material destroyed. Confidential records or devices should be backed up and kept in a fire proof file cabinet. Destruction should be handled appropriately. For purposes of oversight, child protection concerns should be reported at least annually to Board representative by demographic, type, outcomes, response including outside referrals, and policy changes related to abuse prevention. This guidance is based on latest UK statutory guidance and your national laws and requirements may differ. For more information see Audits & Checklists.
A forensic interviewer says, “Always assume your records may be needed for evidence, no matter how small the initial concern or disclosure. Inference should be clearly stated as such and the report should be signed and dated. Any additions or corrections should be added, rather than changed, and signed and dated.”
Q. What’s the role of safety surveys and how do we handle anonymous reporting?
A. Per accreditation standards and the ITFCP allegation protocol, anonymous reports should be taken seriously and result in a transparent and confidential inquiry. Safety surveys such as the sample provided in the ICMEC Environmental Audit should be the last part of your prevention program implemented. School response policies and protocols must be in place with trained staff before you implement surveys or anonymous reporting systems. Inadequate preparation or response can silence victims and escalate harm.
Whether you use an app, regular surveys, or physical drop boxes, student opinion should be considered and young people must trust the process. Ensure students know the variety of responses the school might take and help design your approach. Depending on the child protection concern, response to anonymous disclosure might include social-emotional learning, assemblies, student mediators, safety planning, safe spaces, supervision changes, physical space alterations, etc. Victims sometimes want the abuse to stop without action against the perpetrator. Be transparent about the requirements of local law and school policies and consider the wishes of the victim respectfully.
Q. What rules should govern staff members’ outside contact with students? What are the rules for dual relationships: tutoring, babysitting and family friendships?
A. Dual relationships often exist between staff and students outside school. Teachers may live near student families, coach in a local sports league or belong to the same faith community. Where preexisting or family friendships have arisen, care should be taken that professional boundaries are maintained both in and out of school. Staff members should report these relationships and any shared travel to the child protection designate in order to affirm how the professional code of conduct will be maintained.
In cases where schools have traditions of student babysitting or teacher tutoring outside of school, these practices should be carefully reconsidered and risk assessed. If staff provide tutoring, meetings should happen on school grounds, preferably in a central location, such as library, gym or lobby and be observable and interruptable. It is not sufficient to have two children with one adult in a private classroom. When in doubt, the situation should be subject to risk assessment by the child protection designate.
Q. How do European (GDPR) and local data protection regulations affect student and employee information contained in our central record of child protection concerns?
A. All recordkeeping should include consideration of data protection. The main principle with regard to child protection compliance can be summed up by EU/UK GDPR guidance stating, “Fears about sharing information cannot be allowed to stand in the way of the need to promote the welfare and protect the safety of children.” A detailed discussion of GDPR implications for institutional data retention on low level concerns is available here on portal under Policies & Procedures / International Laws.
Your organization must: know the reason why you’re keeping records about children and/or adults (for example, because they relate to child protection concerns); assess how long you need to keep the records for; and have a plan for how and when the records will be destroyed. To keep personal information secure, you should: compile and label files carefully; keep files containing sensitive or confidential data secure and allow access on a ‘need to know’ basis; keep a log with circumstances around information sharing, consent, if applicable, and name/role, date and content accessed or shared. Note that subject consent is not required for records retained for documented child protection purposes. For more detailed guidance see Records Retention and Storage Guidelines in Audits & Checklists.
Subject access rights means those included may have a right to view the data, but may not dictate the contents. Case information should include fair representation. The recommended length of child protection record retention varies, but further UK guidance suggests ‘until students reach at least 25 years old’. The appropriate response should be to not delete information that may be needed in event of an inquiry without getting specialist advice. A sample data protection policy is available in School Policies.
A child protection expert says, “This is a complex area, so it is most important that the school has a clear policy on retention and follows it consistently.”
The material appearing in these pages is intended for informational purposes and should not be considered legal advice or used as such.